Member-only story
Intrusion Detection System Important Specifications
The performance of an intrusion detection system (IDS) is how well an IDS can detect intrusions in a given network. There are many factors in measuring its performance, but in my opinion a good IDS can detect a variety of attacks, can function on a high traffic, and doesn’t greatly decrease the working performance of the users. It ceases to function as an IDS if it cannot detect, no use if it can’t handle high traffic, and a bother if it just keeps disturbing the users. This is the sixth assignment from my Masters Advanced Network Security Course which has never been published anywhere and I, as the author and copyright holder, license this assignment customized CC-BY-SA where anyone can share, copy, republish, and sell on condition to state my name as the author and notify that the original and open version available here.
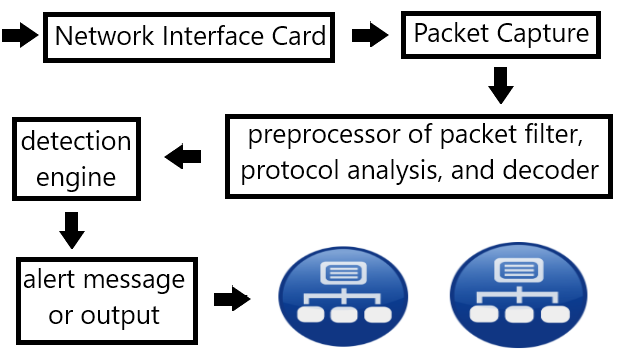
That’s the simple explanation regarding to the IDS but still lots left uncover. To start investigating the performance of an IDS we can first look at the structure of and IDS. For example open source IDS Snort consists of (1) network interface card, (2) packet capture, (3) preprocessor of packet filter, protocol analysis, and decoder, (4) detection engine, and (5) alert message or output. (1) determines how much packet it could receive, (2) and (3) are essential to capture and identify the packets, and (4) itself is the heart of the IDS which determines whether the packet is a threat or not, lastly (5) informs the administrators. When packets goes through (1), (2) (3) and (4) process the packets thus a performance can be measured seeing how much packet it could process, how are dropped, in special cases how much slips the inspection. With these IDS structure many have identified factors that determines the performance if IDS.
- Coverage, is a parameter of how many kinds of attacks it could identify in an ideal environment (theoretically). For signature based IDS is how much attack patterns recorded on the database and for anomaly based IDS is based on the defined ideal networking of the protocol and the traffic.
- Detection capability, a measurement of how well it could detect on certain network configuration and traffic. The deeper the analysis the better that contains the severity of the attack and the outcome attack was successful or not. Even further it could detect…
